Speakers 2023
Come take a look at our exciting list of experts, leaders, and practitioners who are going to give us an amazing conference. If you haven’t bought your ticket yet, you will want to after this!
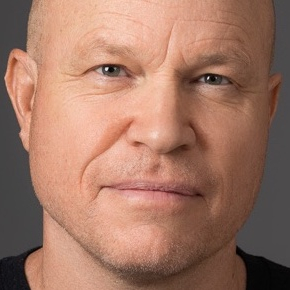
BB King - Keynote Speaker

Keynote: “AI is changing your world, but you will still matter”
Brian “BB” King, GXPN, CEPT, CISSP, GCIH, GCIA
BB has been a Security Consultant at Black Hills Informatin Security since 2015 and a penetration tester since 2008. In previous corporate security roles, he developed application security testing and reporting standards, worked with development teams to improve coding practices, and with new penetration testers to help them gain proficiency and understanding. At BHIS, he specializes in web applications and web APIs, and sees developers and QA engineers as partners in the never-ending quest to make security part of the development lifecycle instead of just a checkpoint near the end. He teaches penetration testing and reporting classes with Antisyphon Training and at local security conferences whenever he can.
Carrie Roberts

Presentation: “10 Hacks to Bypass PowerShell History Log”
Carrie Roberts is a programmer, turned pentester, turned red teamer, turned blue-ish purple. She is currently a Defense Engineer at Walmart. She loves to learn and give back to the community. She is one of the primary Atomic Red Team project maintainers and developers and has developed many of her own open-source tools. She holds master’s Degrees in both Computer Science and Information Security Engineering. She has earned 12 GIAC certifications including the prestigious “Security Expert” (GSE) certification.
Bryan Sears

Presentation: “5 Things to do before your next pentest”
Bryan Sears is a cyber security engineer for Shorepoint inc where he travels the county performing Penetration Test for customers. He is OSCP and CRTO I certified. Bryan is also currently working on his Master’s in Information Security and Information Assurance from WGU. Bryan is also an licensed Official for High School football and Wrestling. While not comprising active directory, He enjoys exploring the trails on his bike or with his Dog.
Edmund Brumaghin

Presentation: “IPFS, DApps, & Blockchains: How Web3 Technologies Are Being Abused In Malware and Phishing Campaigns”
Edmund Brumaghin is a threat researcher with Cisco Talos. He has spent the past several years protecting environments across several different industries including nuclear energy, financial services, etc. He currently spends his days hunting malware and analyzing various threats as they emerge and continue to evolve. In his time with Talos he has researched ransomware, banking trojans and other threats being distributed using various attack vectors. He has also worked to expose large scale malware campaigns and raise awareness of security threats observed across the threat landscape.
Michael Miller

Presentation: “Building Home Labs for Fun & Career Development”
Presentation: “Let’s Talk About Bruno - The Reality of the Cybersecurity Talent Shortage”
Michael is a cybersecurity leader & practitioner with 11+ years’ experience in enterprise cybersecurity, networking, server administration, and programming. Specializing in security architecture, engineering, automation, and operations, he has a proven record of improving team organization, morale, and enhancing cross functional team collaboration while continuously increasing overall company security maturity. Passionately focused on attracting, developing, and retaining talent, he advocates improving diversity, equity, and inclusion in both his teams and the cybersecurity industry. He has a B.S. in Cybersecurity and Information Assurance from WGU, and an A.A.B. in Network Administration and Computer Programming from NSCC where he also sits as a member of the IT advisory board. Michael holds a variety of industry certifications including the CCSP, SSCP, CySA+, CEH, and ECES just to name a few. Michael lives in Northwest Ohio with his wife and their two children. In his free time, he enjoys spending time with his family, cooking (especially grilling), working on home improvement projects, reading, and working in his home networking lab.
Kent Backman
Presentation: “Inside Black Basta Exfiltration Operations”
Kent Backman is a Principal Adversary Hunter at Dragos, specializing in behind-keyboard adversaries to industrial control systems and operational technology. Kent’s expertise has been informed by incident response, digital forensics, threat analysis, and hunting work for government and commercial organizations since 2002.
Matt Fisher & Wren Forfa

Presentation: “The Red and the Blue: A Dual-Sided Analysis of DNS Tunnelling”
Matthew Fisher and Renee (Wren) Forfa graduated from Purdue University in May of 2023 with degrees in Cybersecurity. Matthew studied a second major in Network Engineering Technology, while Wren received a second degree in Russian. They are both commissioned officers in the Department of the Air Force. Matthew has operational and leadership experience in the cyber world as a Security Analyst and from his time at a federally funded research center. Wren has hands-on teaching experience and has researched topics spanning from “Malware Identification and Analysis” to “Linguistic Changes in Russian in Turbulent Times”. Matt and Wren enjoy going camping, playing videogames, and going to the gym!
Fun fact: They got engaged this Spring!
Seif Hateb

Presentation: “Purple Teaming For All”
Seif Hateb is a Security Architect with a passion for excellence and innovation. For over a decade, Seif has been designing and delivering cutting-edge security solutions in the fields of cyber defense, cryptography, security architecture, purple teaming, telco, and OT security. Seif has worked on various projects in the Telecommunications and Healthcare industries, ensuring compliance, risk management, and business continuity. Seif a black belt in judo, which taught him discipline, resilience, and teamwork. Seif is a life-long learner who constantly seeks new challenges and opportunities to grow. Seif is also a mentor, a security professor, and a trainer who loves to share my knowledge and experience with others.
Seif collaborates with diverse teams and stakeholders to design and implement cloud and application security architectures that align with business goals and industry standards. Seif is always eager to learn new technologies and best practices to enhance my expertise and contribute to the security community.
Curtis Brazzell

Presentation: “These Aren’t the Phish You’re Looking For”
Curtis is a local security professional with 17 years of security experience. He holds a CISSP, is the author of the Cybersecurity ABC’s children’s books, and is a researcher and blogger in his free time. He’s provided many defensive and offensive security services for customers over the last 12 years and has a passion for spear-phishing and awareness training.
Matt Hansen

Presentation: “The Journey to Big Tech, from a Small Town”
Matt is a Cloud Solution Architect at Microsoft who focuses on Azure Infrastructure and Security. He has been in the industry for 15 years as an Engineer and Architect, and serves as a Subject Matter Expert, Advisory Committee Member, and as a Professor for Cloud and Security Technologies. Matt holds over 50 industry certifications such as the CCSP, CISSP, Azure Security Engineer, Azure Network Engineer, and has held all versions of the Azure Solutions Architecture Certifications. Matt holds a B.S in Network Engineering and M.S in Engineering Management, and a M.S in Information Systems Security and an Executive Certificate in Cybersecurity Management.
TJ Patterson

Presentation: “Practical Vulnerability Management”
T.J. is an accomplished leader in information security, possessing 15 years of industry experience. He has performed different roles across multiple technical disciplines, providing design, implementation and support of a wide variety of technologies.
While he enjoys finding creative ways to solve complex problems, T.J. is most passionate about developing other practitioners. He also is driven by the opportunity to influence cybersecurity culture in anyone.
T.J. currently serves as the Information Security Officer for a financial institution and is responsible for its information security strategy and its execution across the organization, including digital and paper assets.
When not in the office, you will find T.J. spending time with his family or studying foreign languages. He also has 13+ years of experience playing the drums, and he has played many other musical instruments since childhood.
Chris Saylor

Presentation: “Building a Security Governance Program”
Chris has been in the IT/IS fields about for 25 years, and concentrated in consulting services for the finance and healthcare industries before taking on the Information Security Officer role for Bippus State Bank in 2018.
Christian Ebel-Orr

Presentation: “Cyber Threats and Criminal Trends”
Special Agent Christian Ebel-Orr has been with the Secret Service for 20 years. During that time, he has been assigned to the Counter Assault Team, Presidential Protective Detail, Obama Protective Detail, and the Indianapolis Field Office. He currently manages the Indianapolis Computer Forensics Lab and the Indiana Cyber Fraud Task Force. Previously, he was a police officer in Bloomington, IN for five years.
Chris Harvey

Presentation: “Planting a Tree: The long-game of aligning with the business for support, funding, and staff”
Christopher Harvey is the Assistant Vice President of Technology Architecture and the Chief Information Security Officer (CISO) at Brotherhood Mutual Insurance Company. He has been with Brotherhood Mutual since 1998 and has earned the CPCU designation (Chartered Property Casualty Underwriter). Chris holds a Management Information Systems degree from Ball State University, and is a graduate of General Electric’s ISMP program. He has technical certifications from Microsoft, Novell, Lotus, IBM, and is a Certified Information Security Manager (CISM).
Today Chris oversees various teams at Brotherhood Mutual including Infrastructure, Support Desk, Office Services, Business Intelligence, andDevOps. In his role as CISO, he focuses on ensuring the stability, security, and performance of the company’s information systems. This includes primary oversight of networking, data security, communication services, computer equipment, cloud, and application servers.
